If your organization has gone through the process of an OT cybersecurity risk assessment, you may assume you have a clear understanding of the risks you’re facing. But are you really seeing the full picture?
Too often, companies focus only on gaps. They evaluate their program maturity, review network architectures, search for vulnerabilities, and compare their practices to industry standards and best practices, but they don’t always tie those issues back to how they could actually impact operations.
The result? Companies think they’re doing well, but they’re still exposed to significant operational risks or they are spending resources addressing gaps that will not substantially reduce risk.
If your risk assessment doesn’t consider all three critical elements – threats, vulnerabilities and consequences – you might be missing the most important risks altogether.
The Blind Spots in Most Risk Assessments
Many cybersecurity assessments fall short because they only focus on one or two parts of the puzzle instead of the full picture. Here’s what often gets missed:
- Only looking at external threats: Some assessments zero in on external threats like malware, phishing or hackers accessing the OT environment from the enterprise/business networks but overlook internal threats such as maintenance laptops, accidental misconfiguration errors, and unauthorized wireless access points that can bypass perimeter security controls.
- Assuming compliance equals security: Publishing policies and following standards is important but just because an organization has them in place doesn’t mean they’re properly applied – or that they actually reduce risk.
- Overlooking “double jeopardy” scenarios: Traditional risk models plan for one thing to go wrong at a time. But cyber incidents are intentional. Attackers can, and often do, take down multiple systems at once.
- Focusing on vulnerabilities: Many assessments focus on discovery of vulnerabilities, such as outdated operating systems, known vulnerabilities (i.e., CVEs), weak passwords. Listing vulnerabilities is helpful, but without asking what would happen if the vulnerability was exploited, you’re not actually assessing risk
If you’re not linking security gaps to real operational and financial consequences, it’s almost impossible to know what really matters – or what to fix first.
The Three Elements Every Risk Assessment Should Cover
A truly effective risk assessment goes beyond simple gap analysis. It looks at the full picture by connecting three key elements:
- Threats – What could cause a cyber incident?
- Malware, phishing, ransomware
- Human errors or insider threats
- Unknown or unauthorized devices on your network
- Vulnerabilities – Where are the weak spots?
- Networks without proper separation
- Devices that connect both IT and OT networks
- Policies that are weak – or not followed at all
- Consequences – What happens if something slips through?
- Loss of control over key operations
- Production downtime and financial losses
- Safety hazards, regulatory fines, and environmental impact
All three elements – threats, vulnerabilities and consequences – have to work together to give you the full picture.
Where Traditional Assessments Go Wrong
Many organizations rely on assessments that are valuable but incomplete when it comes to understanding true risk.
- Maturity & gap assessments measure compliance but don’t quantify real risk. They tell you if you have policies in place, but not if they are effective.
- Basic network security reviews focus on configurations but don’t connect security gaps to business impact.
- Lack of prioritization leads to wasted resources. Without understanding which risks have the greatest consequences, organizations often spend money securing the wrong areas.
A Better Way to Connect the Dots: Bowtie Analysis:
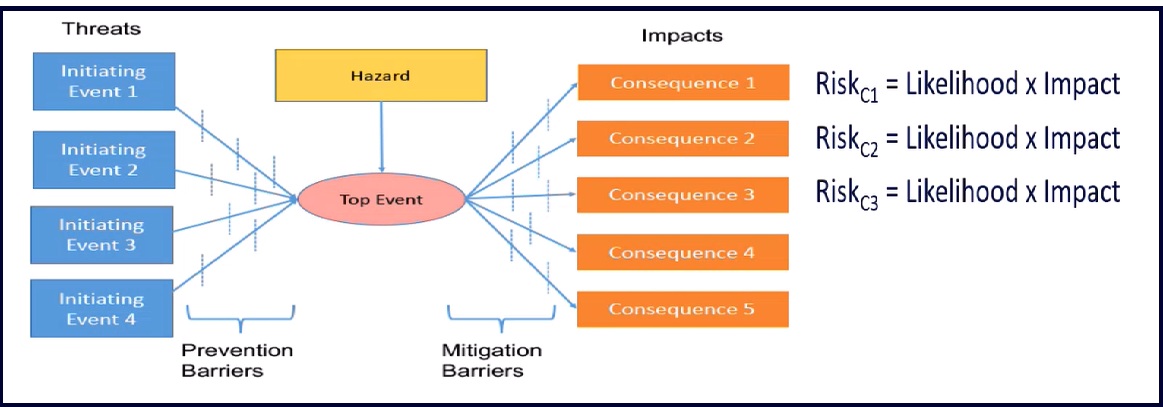
Bowtie Analysis is a visual method that clearly shows how threats, vulnerabilities and consequences are connected in a clear, structured way. It helps teams:
- See how one issue can trigger a chain of events
- Pinpoint which controls matter most, and whether they’re working
- Understand what’s still at risk, even with protection in place
- Meet regulatory expectations with a clear, easy-to-explain model
By mapping out risks in a straightforward, visual way, Bowtie Analysis helps security teams and senior leadership understand where to focus – and where to take action first. Armexa CyberBowtie™
Is It Time to Rethink Your Approach?
If your risk assessment doesn’t connect threats, vulnerabilities and consequences, there’s a good chance some critical gaps are being overlooked. Cyber risk isn’t just an IT issue – it affects operations, finances and most importantly, safety.
A consequence-based approach helps make sure your security efforts actually line up with what matters to the business. It makes it easier to prioritize, reduce high-risk impacts, and avoid expensive surprises.
Your Next Steps:
- Take another look at your most recent risk assessment – did it account for consequences?
- Ask whether your security measures are truly effective – or just written down.
- Consider using Bowtie Analysis to bring clarity to your risk picture and support better decisions.
If you’re looking for more than just a list of issues, Bowtie Analysis helps you see the bigger picture – and what to do about it.
Curious what Bowtie Analysis looks like? We break it down step-by-step in this webinar.
You can find four examples, drawn from actual assessments, where OT security measures weren’t providing the protection companies thought they were in this blog. Your OT Security Measures Look Good on Paper – But Are They Really Working?